Developing awesome applications involve adding the right security measures to the app. Often little security mistakes have caused big companies get out of their businesses. Below are some of the simple steps that can be taken during the android app development cycle to avoid security loopholes.
1) Right platform selection
Choose the right platform and API’s as provided by the android platform. Often there is a security update and updates to the API. Pay attention to the updates. Using the deprecated API’s might lead to back door threats/attacks.
2) Code obfuscation
Make sure to use pro guard to obfuscate the files. This helps in reducing the file size. Also removes the dead code while compiling. Makes reverse engineering the code little complicated.
3) Data security
Data of the customer is so critical to be left at the mobile storage. Ensure the data is stored safely
a) SQLite encryption – Encrypt the SQLite DB for enhanced safety
b) External file storage – Do not write data to any text files unless and until it is not critical.

4) Indefinite login sessions
In the modern-day usage of the app, it is very common to have indefinite session for the customers. Indefinite session on mobile apps are mostly to gain good customer experience. Even in those cases make sure you follow proper security architecture of Anonymous Tokens, Access Tokens and Refresh Tokens.
5) Improper authorization
Grant access to users only based on what role their credentials are entitled to. Improper authorization may lead to unwanted access to the users.
6) Android web views
Unwanted usage of web views might lead to cross-site scripting. Hackers might inject client side scripts to bypass access controls and gain unauthorized access. Avoid redirecting to web views especially when the app is login based.
7) Debug tools
It is common to use lots of debug tools like stetho or Charles proxy. While releasing the build to prod make sure that debugging options are closed. This can be achieved using various build variants. Build variants ensure that we don’t leave the debugging tool left open by mistake.
8) Debugger or logger statements
Seems to be simple. But this can be a very costly mistake that the developers may lead the app to. Leaving the debugger statements enabled in production version of the app will lead the hackers to back track the issues and inject potential threats.
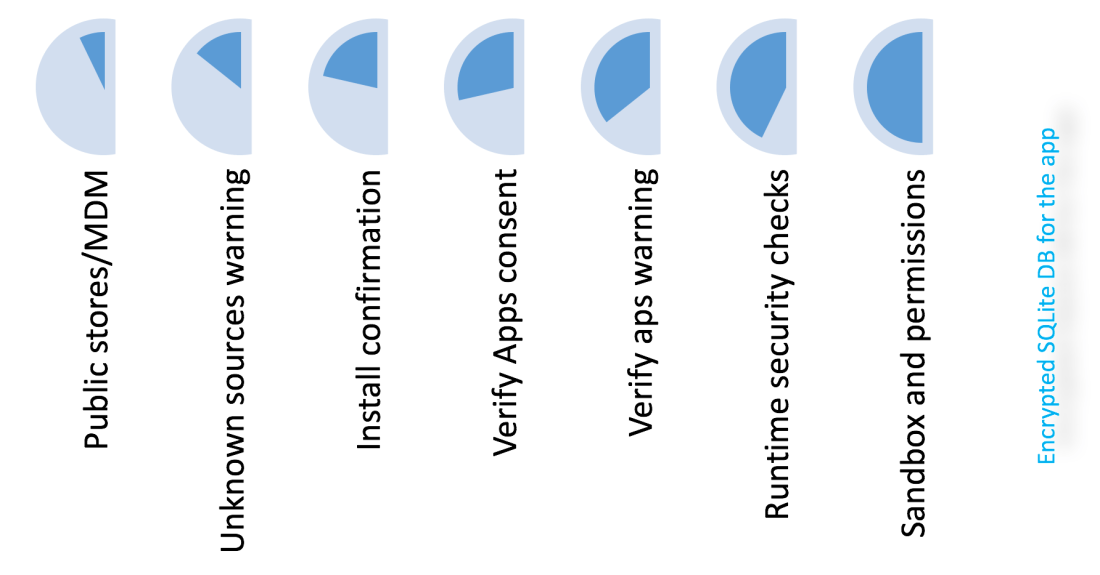
9) Android’s default security architecture
Understand the default security that is being ensured by Google PlayStore during the application review process, before it is being released in the play store. This helps in ensuring security at different layers.
10) Build keys
The build keys of the app should be stored in a secured storage. Discuss with organization’s security team to learn more on where to store the applications build key.
11) Quality gate warnings
Do not ignore the warnings. It is easy to ignore warnings suggested by Lint or SonarQube. Try to resolve the warnings as much as possible before the application is ready to be released in play store
12) Incorrect or Insufficient Cryptography
Make sure that all the data and interaction with server are all secured with proper cryptographic algorithm. However, there might be chances of using small length keys, weak ciphers, incorrect type of crypts or even vulnerability to a known type of crypt-analytic attack. Pay attention to avoid the above.
13) Clean desk policy
As with the traditional policy – do not leave any documents involving algorithms or business intelligence unattended during the development cycle.