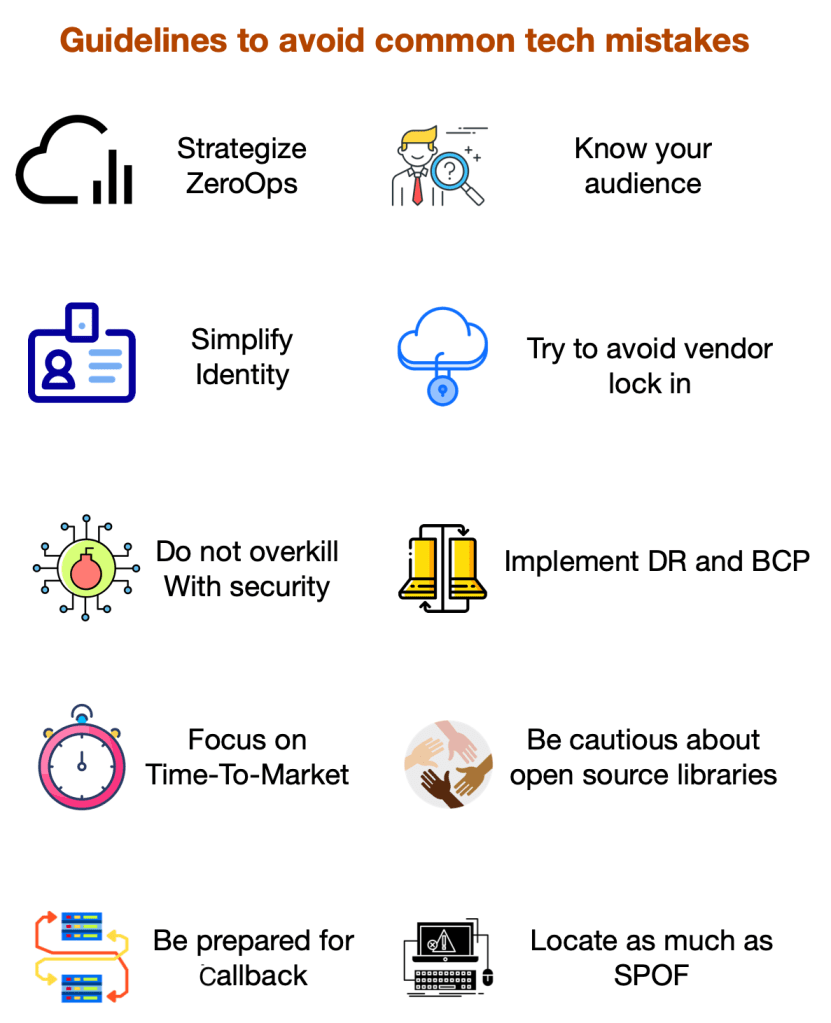
Technology is playing a bigger role in solving today’s human problems. However, choosing the right technology determines a concrete solution. Today’s technologies are evolving very fast. It is advisable to follow general guidelines to avoid common tech mistakes.
1) Know your audience
In today’s world, customers drive businesses. The new features should be loved by your customer. Often this is done by taking the new features with A/B testing. If the testing does not yield the expected results, get the feedback from the users and change/drop the features from getting rolled out to production.
2) Do not overkill with security –
Security is very important for a solution. At the same time do not try to protect every data that is available in the system. Data classification comes in handy to determine authenticated vs unauthenticated access to the systems. Run security scans on the infrastructure and the application to determine any security vulnerability on the system.
3) Focus of GTM –
Time to market is crucial to deliver the new idea to the customer before the competitor rolls out. Identifying the right metrics, setting the target audience, figuring out the rollout strategy should be derived from the unified analytics engine. Collecting market-driven feedback helps in adopting a continuous improvement strategy for the product.
4) Try to Avoid vendor lock-in –
Many times, the solution is built by stitching other small domain focussed solutions. This will create a vendor lock-in one way or the other. Often there is decision-making over buy vs build.
A) Buy – Try as much as possible to have a backup plan for a chosen vendor.
B) Build – Try to be cloud-agnostic while choosing the resources within the cloud
5) Be cautious about open source libraries-
Rapid application development is made easy by utilizing open source libraries. We discussed security being overkill. However, having a very tight security scan on the libraries is needed. Increasing the scans gives early access to the vulnerabilities before it is rolled out to the customer without affecting the performance of the application.
6) Strategize ZeroOps –
If taking the product to the customer at the right time with the rapid application development tools is important, supporting the product by providing operational support is the other part of the work. Work to implement self-heal and high available system architecture by utilizing modern cloud solutions like serverless architecture.
7) Locate as much as SPOF –
Highly available systems have near-zero single point of failures. It is not possible to build a system with Zero SPOF. However, graceful handling of the user experience should be considered. One way to determine reduction is by ensuring less RTO and RPO of the deployed application.
8) Simplified identity –
Identity and access management is needed for the users to use the application. The application can be customer-facing or can be a back-office tool used by employees or as development consoles used by the developers. Evaluate the risk level of the application and then enforce the needed identity, rather than treating all the applications with the same identity standards.
9) Implement DR and BCP –
With an increased rush to deliver the product to the market, many times we miss focussing on business continuity plan and disaster recovery. The modern serverless architectures in the cloud help in preparing DR and BCP plans with zero upfront cost. While working with multiple providers, ensure that the SaaS solution is highly available.
10) Be prepared for fallback –
At last, when the tech system fails (which may not happen), be prepared to handle your customers in an alternative channel. This can be achieved by asking questions like –
- What are the different ways the customer interacts with the business?
- Are we having failover systems in place? and so on
Share your thoughts and experience around building systems with minimalistic tech mistakes.
Happy learning!